A burner account is an anonymous or secondary online profile used to browse, post, or interact without revealing a user’s real identity. In today’s digital landscape, where online and offline identities often overlap, these accounts offer both privacy benefits and potential risks. They are used by individuals—including public figures—for discreet communication, but are also linked to cyberbullying, misinformation, and harassment.
But what exactly is a burner account? How are they created, and why should businesses, schools, and even governments care? This blog dives deep into the burner account meaning, legal concerns, usage scenarios, and the crucial role of social media screening in detecting them.
What Is a Burner Account?
A burner account is a secondary or temporary online profile, typically created on social media platforms, to hide a user’s real identity. These accounts are set up using disposable email addresses or temporary phone numbers, enabling anonymous activity with minimal traceability.
In simple terms:
If you’re wondering, “what is a burner account on social media?”—it refers to an account used to browse, comment, message, or post without linking back to a primary identity. Burner accounts are commonly used for privacy, anonymous engagement, or, in some cases, to avoid accountability while interacting online.
Why Do People Create Burner Accounts?
Burner accounts are secondary, anonymous profiles created for both legitimate and risky purposes. Understanding user intent helps organizations assess potential threats and ethical concerns.
1. Privacy and Anonymous Browsing
Many users create temporary or alternate accounts to explore content without tracking, personalization, or linking activity to their real identity.
2. Harassment and Trolling Risks
Burner accounts are frequently used for cyberbullying, spreading misinformation, or engaging in harmful discussions, as anonymity reduces accountability.
3. Bypassing Bans or Blocks
Users who are banned or blocked often create new anonymous accounts to regain access and continue activity on the platform.
4. Student or Parental Surveillance
In the context of student vetting, schools and immigration bodies are increasingly paying attention to secret accounts that applicants might use to post problematic content.
🔍 Pro Tip: Use automated social media safety checks to detect secret or alternate accounts when reviewing student visa applications.
Read more:
How to Create a Winning Social Media Listening Report
Social Media Listening and Analytics: How to Turn Insights Into Strategy
Free Social Media Listening Tools: How To Get Started Without a Budget
Social Media Listening Tools Comparison: Feature Breakdown and User Ratings
How Are Burner Accounts Created?
Creating a burner account is relatively simple and requires minimal technical expertise. It typically involves three key steps:
1. Disposable Email Setup
Users begin by generating a temporary email through services like ProtonMail, TempMail, or Gmail. These emails require little to no personal identification, ensuring anonymity.
2. Anonymous Phone Verification
To bypass platform verification, users rely on virtual number services such as TextNow or Google Voice. Others may use prepaid SIM cards or purchase untraceable numbers, enabling account creation without linking personal data.
3. Generic or Fake Profile Creation
Finally, users set up profiles using vague or non-identifiable usernames (e.g., @hidden_ghost or @throwawaythoughts). These profiles often lack real photos or details, making attribution difficult.
Are Burner Accounts Traceable?
Burner accounts are not fully anonymous. While they hide identity, digital footprints—such as IP addresses, device data, and platform activity—can enable tracing. Law enforcement, platforms, and cybersecurity experts can often identify users under specific legal or investigative conditions.
Can Burner Apps Be Traced?
1. Traceability
Burner apps and numbers can be traced, but only with advanced methods.
2. Access Required
Typically needs legal action or law enforcement involvement.
3. Limitations
Individuals (e.g., recruiters, school admins) cannot trace them independently.
4. Best Approach
Use Phyllo’s social media screening tools to identify suspicious or anonymous activity effectively.
How to Identify a Twitter Account Owner?
Use social media listening and background verification tools to analyze patterns such as content, location, behavior, and linked profiles. Solutions like Phyllo’s Background Verification API help uncover connections and detect potentially risky digital footprints with greater accuracy.
Read more:
Social Media Screening for Employment: The Impact on Hiring Decisions
20 Types of Red Flag Behavior Found on Social Media Background Checks
How to Measure Quality of Hire: 7 Key Metrics That Reveal Hiring Success
Types of Burner Accounts by Platform
Burner accounts differ across platforms based on visibility, anonymity, and ease of detection.
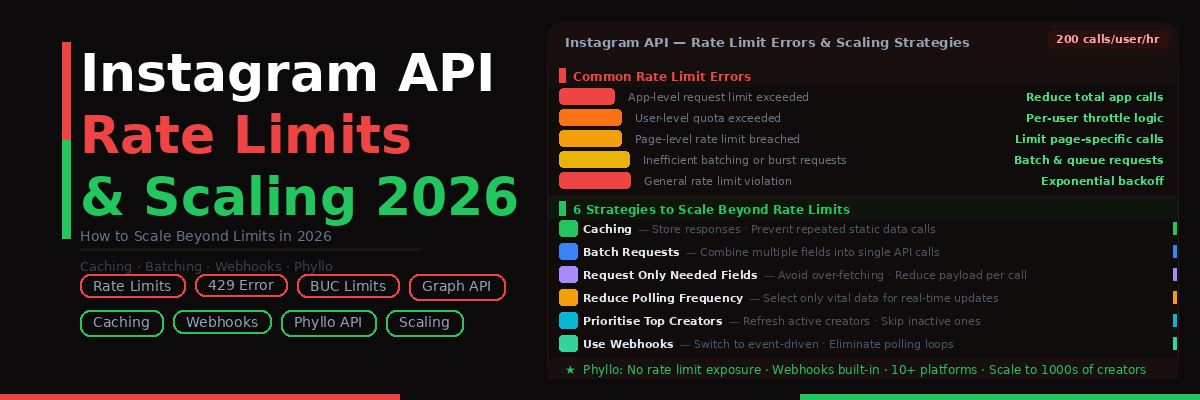
1. Instagram
Commonly used for anonymous browsing, stalking, or trolling. These accounts are often short-lived and created with temporary emails or phone numbers.
2. Twitter/X
Designed for high anonymity, these accounts are frequently used for sharing opinions, memes, venting, or harassment. Users may rely on VPNs and fake credentials to reduce traceability.
3. TikTok & Facebook
Less prevalent due to stricter identity policies and algorithmic monitoring, yet still used for passive viewing or subtle engagement without revealing identity.
Understanding these variations helps identify risks and strengthens social media monitoring strategies.
While some view burner accounts as harmless, they pose significant risks—both for users and institutions.
Risks of Burner Accounts
Burner accounts may seem harmless, but they create serious risks for individuals and organizations.
For Individuals
- Exposure of identity and loss of anonymity
- Legal consequences from cyberbullying or misuse
- Platform penalties such as bans or shadowbanning
- Long-term damage to personal and professional reputation
For Employers and Schools
- Hiring or admitting individuals with harmful online behavior
- Legal liability from overlooked digital red flags
- Reputational damage if anonymous activity is later uncovered
Use social media screening tools to protect your organization from bad hires or damaging partnerships.
Use Cases Where Burner Accounts Are Detected
Burner accounts are frequently identified in high-risk screening and investigative scenarios where identity verification is critical.
1. Hiring and Employment
Anonymous profiles may expose discriminatory, abusive, or unethical behavior not visible in resumes or interviews, helping employers make safer hiring decisions.
2. University Admissions & Immigration
Undisclosed online activity or controversial content shared via alternate accounts can impact admissions or visa approvals. Student vetting tools can help assess such risks effectively.
3. Legal Investigations
Authorities use digital forensics and platform data requests to trace anonymous accounts linked to fraud, harassment, or other serious offenses.
How to Spot a Burner Account?
Identifying a burner account can be challenging, but common patterns help. Look for profiles with few or no followers, recent creation dates, and minimal personal details. Other warning signs include vague or suspicious usernames, aggressive or anonymous interactions, and repetitive posting behavior across multiple accounts, indicating potential inauthentic or coordinated activity.
Tip: Use social media listening to track patterns and flag anomalies in user behavior.
Proactively protecting your business or school from burner account risks is possible with the right tools and policies.
How to Protect Your Brand from Burner Accounts?
Protecting your business or institution from burner account risks requires a proactive, structured approach combining technology, education, and policy enforcement.
Key Strategies:
- Social Media Screening: Use automated social media background screening tools to identify duplicate or suspicious profiles and detect content inconsistencies during hiring or onboarding.
- Awareness & Training: Educate employees, students, or stakeholders on the legal, ethical, and reputational risks associated with anonymous accounts.
- Active Monitoring: Implement social listening tools to track brand mentions, sentiment shifts, and unusual activity patterns that may signal burner account misuse.
- Clear Digital Policies: Establish and enforce guidelines for acceptable online behavior, ensuring accountability even outside formal environments.
Adopting these measures strengthens digital safety, protects reputation, and ensures compliance with evolving online risk standards.
Burner Accounts and Digital Identity Ethics
Burner accounts can protect anonymity for legitimate users like whistleblowers and activists, but they also reduce accountability and increase misuse risks. As AI-powered screening becomes widespread, ethical boundaries are critical. Organizations should adopt privacy-first solutions—such as consent-based data tools—to balance user rights with accurate risk detection and compliance with global data protection laws.
FAQs About Burner Accounts:
1. What’s a burner number?
A burner number is a temporary, often untraceable phone number used to sign up for apps or communicate without revealing your real phone number.
2. Can burner phones be traced?
Yes, but it's difficult. Tracing typically requires legal action, subpoenas, or access to mobile carrier data.
3. Are burner numbers traceable?
Some are traceable depending on the app or service used. Apps that don't require ID make tracking more difficult.
4. What is a burner account on social media?
It’s a fake or secondary account used anonymously for browsing, posting, or interacting online without linking it to the user’s real identity.
5. How to trace a burner phone?
This usually involves telecom service providers and law enforcement. Some apps log IP addresses which can help in investigations.
6. Can a burner app be traced?
Many apps claim to offer anonymity, but some store user data like IP, device ID, and activity logs, which can be subpoenaed.
7. How to get an anonymous phone number?
Use apps like Burner, TextNow, or Google Voice. However, true anonymity is difficult unless you avoid linking the number to any personal data.
8. What’s the best burner email service?
Popular burner email services include ProtonMail, TempMail, Guerrilla Mail, and Mailinator.
Final Thoughts
Burner accounts are more than just tools for trolls or secret stalkers—they’re a growing part of digital behavior, with implications for hiring, security, ethics, and reputation. Whether you’re a recruiter, an admissions officer, or a business owner, understanding the signs of burner activity is essential to protecting your organization.
Using tools like Phyllo's social media screening, student vetting, and social listening APIs can give you the transparency needed in an increasingly anonymous digital world.









.avif)
.avif)
